
AI-First Universities: Salesforce Education Cloud & Agentforce
Discover how Salesforce Education Cloud, Data Cloud, and Agentforce enable AI-driven student engagement and intelligent campuses with Altimetrik.

From Checkout to Cloud — Rethinking Security for the Modern Retail Enterprise
Retail cybersecurity has never faced a more complex threat environment. Consider what a large retail organisation today actually is.
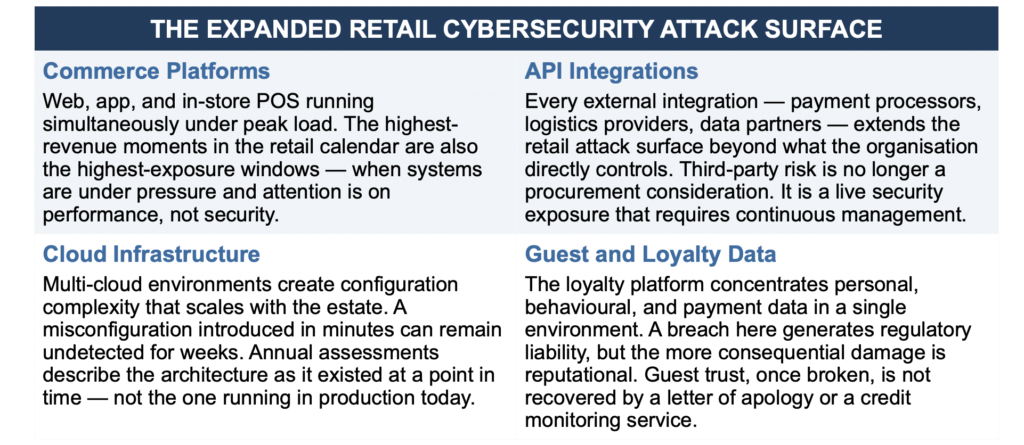
Not a store, or even a chain of stores. A loyalty platform holding tens of millions of member profiles. Several hundred live API connections to payment processors, fulfilment partners, and data providers across multiple geographies. Cloud infrastructure spread across two or three major providers, running workloads that touch guest data around the clock. Stores operating on devices that share network architecture with payment systems.
And layered on top of all of it, a commerce experience that has to perform flawlessly during the exact moments product launches, seasonal peaks, exclusive member events when every system is under its highest load simultaneously.
That is not a retailer in the traditional sense. That is a technology company operating in retail. And it carries the security obligations of one.
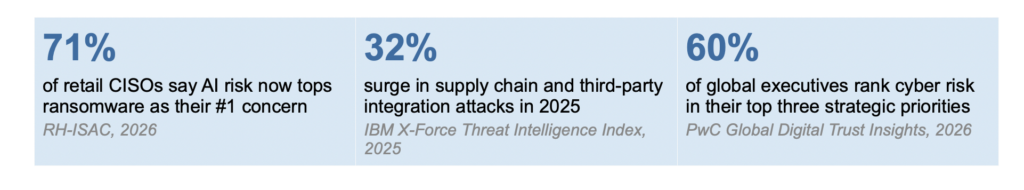
This is the tension at the heart of retail cybersecurity in 2026. The commercial transformation has been real, substantial, and largely successful. The security architecture, in too many cases, has not kept pace. Not for lack of investment. Not for lack of awareness. The gap is structural security models designed for a bounded, relatively static environment being asked to protect one that is distributed, interconnected, and changing every week.
Retail did not become more vulnerable because it became less careful. It became more vulnerable because it became more connected and the security architecture that was built in a previous era was never designed to protect what retail has become.
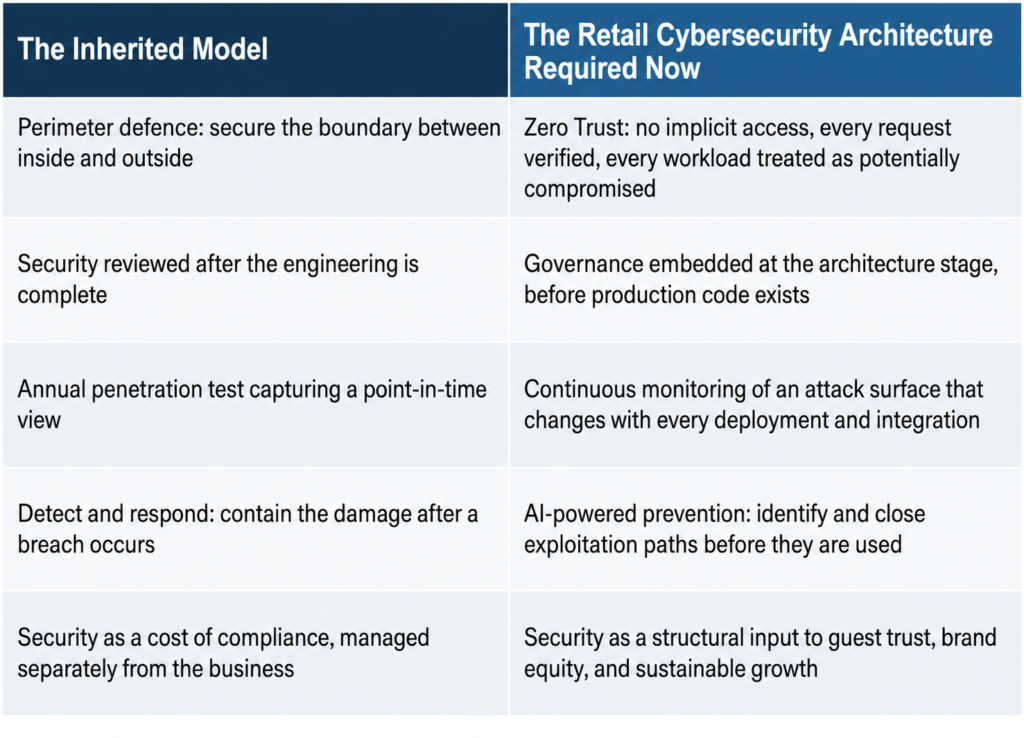
For most of the 2000s and 2010s, enterprise security operated on a coherent set of assumptions. The enterprise had a perimeter. Users and systems inside it were trusted. Threats came from outside. The job of security was to defend the boundary.
Each of those assumptions has been invalidated by the way modern retail operates. The perimeter dissolved when loyalty platforms went cloud-native and fulfilment became a network of third-party partners. The inside/outside distinction became meaningless when store associates started using mobile devices on the same infrastructure as payment systems. The retail cybersecurity threat model shifted when attackers realised that the most valuable targets member databases, payment infrastructure, commerce platforms were often better reached through a supplier’s misconfigured API than through a direct assault on the retailer’s own systems.
Today’s retail attacker is patient, opportunistic, and increasingly AI-assisted. They do not look for the weakest point in a perimeter. They map the entire ecosystem every integration, every partner access credential, every cloud misconfiguration and find the path of least resistance to the data that has the most value. A loyalty platform combining identity, behavioural, and payment data in a single place is worth considerable effort. So is a peak trading event, when the pressure to keep systems running creates exactly the conditions under which security shortcuts are most likely.
When a retail security incident makes the headlines, the coverage focuses on the regulatory fine, the forensic investigation, and the cost of remediation. These are real and significant. They are also the visible fraction of the total cost.
The more consequential damage accumulates quietly, over months, in the behavioural data that loyalty and commerce platforms are built to track. How many members quietly stopped using the app after the incident? What happened to repeat purchase frequency in the affected cohort? How did average order value shift among guests who received the breach notification?
These numbers are rarely disclosed, but they are significant and unlike a one-time fine, they compound. A guest who loses confidence in how a brand manages their data does not just reduce their next purchase. They reassess the entire relationship.
This is the dimension of retail cybersecurity that deserves more attention in the boardroom. The loyalty economy that retail has spent a decade building rests on a specific exchange: a guest shares their data, their preferences, their purchase history, and in return receives a more personalised, more seamless experience. That exchange is a trust agreement. Security is the operational infrastructure that makes it possible to honour that agreement at scale. When it fails, the brand pays in the currency it spent years accumulating.
A loyalty breach is not primarily a legal event. It is a relationship event. The fine has a defined ceiling. The trust does not.
The natural response to a retail cybersecurity gap is to invest more in security. More tools, more headcount, more sophisticated detection. This response is understandable, and some of it is necessary. But it addresses the symptom rather than the structural problem.
The structural problem is that the traditional security model was not designed for how modern retail operates. Perimeter defence assumes a bounded environment. Annual audits assume a relatively static system. Reactive detection assumes that the time between an incident and its discovery is short enough to limit damage. None of those assumptions hold in a retail estate that spans hundreds of API integrations, multiple cloud environments, and stores in several countries, all of which are changing continuously.
The organisations that have genuinely closed the retail cybersecurity gap have not just spent more. They have made a different architectural decision: security is not a layer applied on top of the engineering organisation. It is a property of how the engineering organisation works.
That shift changes when governance happens, how deployment pipelines are structured, who owns security posture for a given system, and what it means for security to be “done.” The difference in outcomes between these two models is not marginal.
Retail has built something genuinely impressive over the past decade. The digital commerce experience, the loyalty infrastructure, the supply chain intelligence running behind every personalised interaction: these represent real capability, real investment, and real competitive advantage. They also represent a retail attack surface of a scale and complexity that grows with every new integration, every new market, every new digital experience added to the estate.
The organisations navigating this well are not distinguished by how much they spend on security. They are distinguished by when they made the architectural decisions that matter: before the first deployment, not after the first incident. Before the breach, not in its aftermath. Before the trust was lost, not in an attempt to recover what was once taken for granted.
The question worth asking is a simple one. Does the retail cybersecurity architecture protecting this organisation reflect the organisation as it exists today distributed, connected, fast-moving, and deeply reliant on guest trust? Or does it reflect the organisation as it existed when the architecture was last designed?
The answer to that question is more important than any specific technology decision. And in most cases, the honest answer points to work that needs to be done.
Security is no longer the function that protects the business from the outside. It is the function that makes growth possible from the inside.

Discover how Salesforce Education Cloud, Data Cloud, and Agentforce enable AI-driven student engagement and intelligent campuses with Altimetrik.

Learn how a fragmented call center evolved into an intelligent service platform, boosting operational efficiency, enhancing customer experience, and delivering actionable insights at scale.

Regional banks are under pressure to improve operating economics without taking on avoidable transformation risk. The FDIC said industry net income fell 2.0 percent quarter over quarter in Q4 2025, driven mainly by higher noninterest expense, while the OCC warned that prolonged use of legacy systems can increase outages, security vulnerabilities, maintenance challenges, and resilience […]
Altimetrik is committed to protecting your personal information. To apply for a position, you will need to provide your email address and create a login. Your information will be used in accordance with applicable data privacy laws, our Privacy Policy, and our Privacy Notice.
