
AI-First Universities: Salesforce Education Cloud & Agentforce
Discover how Salesforce Education Cloud, Data Cloud, and Agentforce enable AI-driven student engagement and intelligent campuses with Altimetrik.

In today’s fast-evolving cybersecurity landscape, businesses rely on Vulnerability Management Systems (VMS) to identify, assess, and mitigate risks. However, commercial VMS solutions come with inherent problems that limit their efficiency and adaptability. Organizations seeking greater flexibility and control are now exploring custom-built alternatives tailored to their specific needs.
Before we dive into why organizations today need a custom VMS platform, lets understand the pain points of the security teams today and how security platforms have played a critical role in better cybersecurity management.
As per IBM Institute of Business Value (https://www.ibm.com/thought-leadership/institute-business-value/en-us/report/unified-cybersecurity-platform) an average organization has 83 security tools from 29 vendors with 52 % of executives saying that the biggest impediment to security operations is complexity. Making a strong case for unifying security operations under security platforms, the article further elaborates on the positive impact on efficiency, with organizations which adopt security platforms reporting 72 days less in detecting a security incident and 84 days less in solving the security incident.
With security platforms that integrate multiple tools and automate security processes bringing better ROI along with better risk visibility and mitigation, organizations that decide to go with Platform solutions are broadly faced with two choices – to buy a commercial VMS solution or develop a custom VMS solution tailored to their unique needs.
Many commercial VMS platforms fail to meet the dynamic security requirements of modern enterprises. Some common problems include:
A custom-built Vulnerability Management Platform (VMP) offers significant advantages over off-the-shelf solutions with following key advantages-:
In many organizations, commercial VMS platforms introduce operational friction due to limited integration flexibility and rigid data models. Security teams often need to reconcile outputs from multiple tools, deal with inconsistent tagging, and manage workflows that don’t scale. A custom VMS eliminates these barriers by design.
Importantly, custom VMS solutions evolve alongside the business. They can accommodate new threat models, onboarding processes, and compliance frameworks without having to wait for vendor releases or reconfigure generic features.
Potential buyers of custom VMS solutions include but are not limited to, enterprises with complex security requirements like:
If your security operations are constrained by the limitations of off-the-shelf tooling or you’re managing a fast-evolving environment with specialized needs, then a custom VMS is more than a tactical investment. It’s a strategic enabler of risk governance and engineering efficiency.
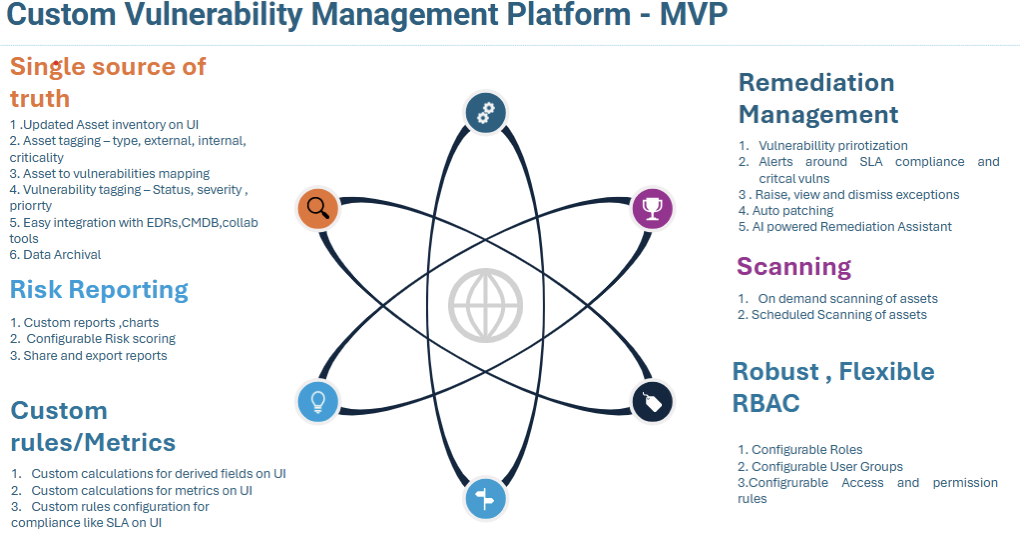
The foundation of a robust custom VMS lies in its core features. An MVP should include the following capabilities:
As cybersecurity threats grow more sophisticated, organizations need smarter, adaptable, and cost-effective vulnerability management solutions. A custom-built VMS provides the flexibility and control required to meet evolving security challenges while enhancing operational efficiency.
Investing in a tailored vulnerability management platform ensures businesses stay ahead of threats, optimize security workflows, and maintain compliance with industry regulations. With AI-driven automation and configurable security controls, a custom VMS is a game-changer in modern cybersecurity strategies.
At Altimetrik, we’ve designed and delivered these solutions for Fortune 500 clients—seamlessly integrating across fragmented environments, normalizing risk data, and enabling real-time response actions. Our offerings are now available via AWS Marketplace, making them easier to deploy and scale.
Are you considering a custom VMS for your organization? Contact us today to learn how a tailor-made solution can transform your vulnerability management approach!
What are the key approaches to cybersecurity?
The three main approaches are prevention (stopping attacks), detection (finding threats quickly), and response (fixing the damage). A strong strategy combines all three for continuous protection.
Which cybersecurity approach delivers the most value?
An integrated, all-in-one platform provides the most value. It’s more efficient and effective than managing many separate, disconnected security tools.
What are the fundamental principles of cybersecurity?
The core principles are Confidentiality (keeping data private), Integrity (ensuring data is accurate), and Availability (making sure systems are accessible), along with accountability and resilience.
What’s the most effective tool for managing vulnerabilities?
The best tool is one that fits your specific environment. A flexible, automated system that integrates with your existing tools offers the most effective way to manage security weaknesses.

Discover how Salesforce Education Cloud, Data Cloud, and Agentforce enable AI-driven student engagement and intelligent campuses with Altimetrik.

Learn how a fragmented call center evolved into an intelligent service platform, boosting operational efficiency, enhancing customer experience, and delivering actionable insights at scale.

Regional banks are under pressure to improve operating economics without taking on avoidable transformation risk. The FDIC said industry net income fell 2.0 percent quarter over quarter in Q4 2025, driven mainly by higher noninterest expense, while the OCC warned that prolonged use of legacy systems can increase outages, security vulnerabilities, maintenance challenges, and resilience […]
Altimetrik is committed to protecting your personal information. To apply for a position, you will need to provide your email address and create a login. Your information will be used in accordance with applicable data privacy laws, our Privacy Policy, and our Privacy Notice.
